What the DealerBuilt Hack Means for P&A
The FTC’s proposed consent order with dealer software provider DealerBuilt settles charges relating to a major loss of customer data, but the conversation over the compliance responsibilities of ‘service providers’ — including those in the P&A segment — is just beginning.

The FTC’s proposed consent order with dealer software provider DealerBuilt settles charges relating to a major loss of customer data, but the conversation over the compliance responsibilities of ‘service providers’ — including those in the P&A segment — is just beginning.
Photo by HYWARDS via Getty Images
The Federal Trade Commission recently issued a proposed consent order against LightYear Dealer Technologies, better known as DealerBuilt. By the time you read this, that consent order will probably be finalized. What did it say and what does it mean for dealers — and for F&I product providers and administrators?
The Hack
DealerBuilt is a company that was, well, built by dealers. It develops and sells dealership management system software and data processing services to automobile dealerships across the country. That DMS tracks, manages and stores both customer and employee data, including an enormous amount of nonpublic personal information.
The customer and employee NPI that routinely runs through the DealerBuilt DMS includes:
Name
Gender
Physical and mailing address
Phone number
Email address
Date of birth
Social Security number
Driver license number
Vehicles owned (identified by license plate number, VIN, and key code)
Credit card numbers
The DealerBuilt DMS is used in approximately 320 dealership locations. Dealership customers licensed the DMS software and either had DealerBuilt host the data or hosted it locally on their own servers. For those that hosted the data locally, that data would be regularly backed up to the DealerBuilt servers. Thus, in either case, DealerBuilt would have virtually all of its users’ data present on its servers.
The FTC’s investigation revealed all of the NPI was stored in clear text, without any access controls or authentication protections (such as passwords). DealerBuilt routinely transmitted the data between servers at the dealership and its backup servers in clear text.
In the spring of 2015 — in order to increase capacity — DealerBuilt personnel added a large storage device to its existing backup network. Unfortunately, that device was not configured securely, and created an open connection port for approximately 18 months.
And what, exactly, is an “open connection port”? It’s a little like a screen door on a submarine: Pretty much anything can get in — and out.
Mr. Hacker successfully downloaded the NPI of 69,283 consumers, representing the entire backup directories of five dealership customers.
For those 18 months, DealerBuilt did not perform any vulnerability scanning or penetration testing that could have discovered the open connection port. Eventually it was exploited, resulting in a major loss of customer and employee NPI.
In late October 2015, and for at least 10 days, a hacker gained access to the DealerBuilt backup database through the open connection port. That database included the NPI of 12.5 million consumers. During that time, Mr. Hacker successfully downloaded the NPI of 69,283 consumers, representing the entire backup directories of five dealership customers.
In a nutshell, the FTC concluded that DealerBuilt’s failure to provide reasonable security for consumer NPI caused substantial harm to consumers (and the dealerships that used the DealerBuilt DMS) in the form of fraud, identity theft, monetary loss, and time spent remedying the problem.
The Safeguards Rule
Here’s where things get interesting. Since May 23, 2003, “financial institutions” have been subject to the federal Safeguards Rule. Most dealerships are “financial institutions” because they originate “covered accounts” such as installment sale contracts and leases.
What’s interesting from DealerBuilt’s perspective is that it, too, falls within the rule’s definition of financial institution. Why? Because it processes data, and if “the data to be processed, stored or furnished are financial, banking or economic; and the hardware provided in connection therewith is offered only in conjunction with software designed and marketed for the processing, storage and transmission of financial, banking, or economic data,” you’re a “financial institution” within the meaning of the Safeguards Rule.
So why is that interesting? Because, DealerBuilt also fits the definition of “service provider” under the rule. Entities covered by the rule are required by its terms to only do business with service providers that can, and are bound by contract to, follow the Safeguards Rule.
Read: Providers, Administrators, and the Safeguards Rule
So if the FTC viewed DealerBuilt in its capacity as a service provider, the FTC would not have gone after DealerBuilt — but it could have gone after the 268 dealership locations that violated the rule by using DealerBuilt without confirming it was complying with the rule. Instead, the FTC viewed DealerBuilt in its role as a financial institution to which the Safeguards Rule applied in the first instance.
Obviously, the FTC chose one action against a single respondent rather than 268 against individual dealerships. We call that “judicial economy.” But there are lessons to be learned from the case beyond just who got sued, and why.
The Big Takeaway
Here’s the big takeaway:
If DealerBuilt was a service provider; and
It failed to follow the Safeguards Rule; then
Every dealership that used DealerBuilt could be liable for failing to follow the Safeguards Rule by using a non-compliant service provider.
Let’s take this logic one step further:
If product providers and administrators are service providers; and
They fail to follow the Safeguards Rule; then
Every dealership that uses that provider or administrator could be liable for failing to follow the Safeguards Rule by using a non-compliant service provider.
Most providers and administrators aren’t “data processors” in the sense DealerBuilt is. Thus, most providers and administrators aren’t “financial institutions” directly covered by the Safeguards Rule. But all are service providers.
As service providers, the DealerBuilt case demonstrates that product providers and administrators are in a fine position to expose their dealership clients to extremely costly legal liability.
What to Do
As the DealerBuilt case implies, providers and administrators can be the cause of tremendous liability on the part of their dealership clients. This is obviously bad for business. What should providers and administrators do?
The first step is to ensure that you are, in fact, following the terms of the Safeguards Rule. And while you’re at it, review the proposed revisions to the Safeguards Rule, available online at GovInfo.gov. Depending on your perspective, the new version will be either more effective or more onerous, and probably both. But that new version is likely to become effective not long after you’ve read this, so prudence dictates preparing for it now.
The second step is to confirm that your dealer agreements include a clause obligating you to comply with the terms of the Safeguards Rule. You might also want to include in the “representations and certifications” section of your dealer agreement a representation that you do, in fact, follow the rule. You might even enumerate some of the steps you take in furtherance of that representation.
Better yet, you could have a separate, standalone “data security agreement” that spells out exactly what you will do to meet the requirements of the Safeguards Rule and otherwise protect client and customer data.
This topic is important enough to have its own contract, rather than just a passing mention in your dealer agreement. But whether it’s a small mention in a dealer agreement, or a more thorough discussion in a document of its own, it must be addressed by contract. It’s not an option — it’s the law, and you have an obligation to help your dealerships comply with it.
Finally, be aggressive with respect to data security. The Safeguards Rule is designed to make that posture mandatory, but it’s tough to legislate “tone from the top.” The senior levels of providers’ management need to be passionate about this. The downside for your client dealerships is too serious for anything less.
James S. Ganther Esq. is the co-founder and CEO of Mosaic Compliance Services. He is a dealer compliance expert and a prolific writer and speaker. Email him at jim.ganther@bobit.com.
More Compliance

What to Expect in 2026 - New Rules and Regulations on the Horizon
In Trump’s first year, just 60,917 pages were printed in the Federal Register, the official journal of the federal government, down 42%.
Read More →

Fines of the Times
Civil penalties for noncompliance with federal auto retail and finance rules and regulations can add up quickly. Use this checklist to cover your bases.
Read More →
Cyber Threats Continue Apace
Hackers, seeing auto retail vulnerabilities in 2024 CDK incident, are taking advantage, data show.
Read More →
Your Synthetic ID Theft Policy
Frankenstein’s monster is coming for your dealership. Use this guide to recognize synthetic ID thieves and maintain Red Flags Rule compliance.
Read More →
The Regulatory Empire Is Striking Back
President Trump - entropist and corporate disruptor in consumer law
Read More →
How to Clear a Red Flag
Refine and enforce your dealership’s FTC-mandated ID theft-prevention program to ensure no transaction goes awry.
Read More →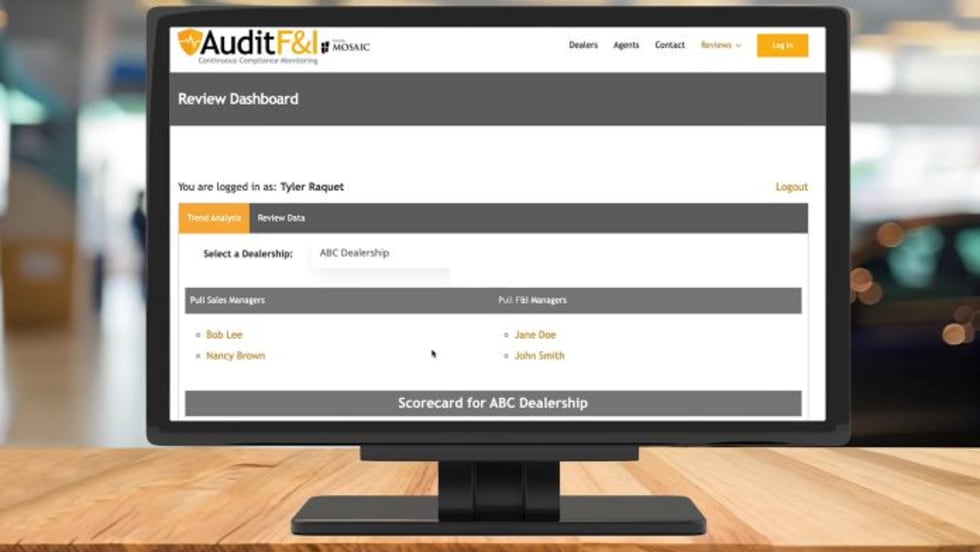
Mosaic Adds Continuous Monitoring With AuditF&I
New AuditF&I platform is designed to give dealerships a smarter way to stay compliant.
Read More →


